The Air Force keeps electronic eyes peeled for sniffers, phishers, spoofers, and hackers.
To defend the full Air Force Network (AFNET)—which the service uses for daily business such as emails and file sharing—the 33rd Network Warfare Squadron operates and relies on a special sidekick: the Air Force Cyberspace Defense (ACD) weapon system.
The custom-built suite of devices and programs is deployed throughout the AFNET ecosystem, always watching it, ever reactive to suspicious activity.
The squadron opens more than 1,000 such investigations each year.
Capt. Anthony Rodriguez, 33rd NWS director of operations at JBSA-Lackland, Texas, recently explained to Air Force Magazine exactly what each of the nine threat categories mean and what happens when ACD triggers them. The Air Force Cyberspace Defense system may resolve issues itself or it may alert a cyber warrior. When an airman gets involved, he or she will investigate to get a better understanding of what’s happened (these are called events) or get up and react to an ongoing and potentially dangerous situation (these are called incidents).
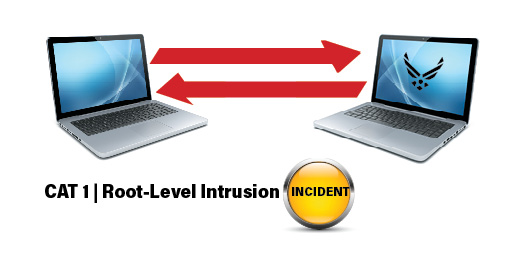
Official Definition
Unauthorized, privileged access to an Air Force system. Privileged access—often referred to as administrative or root access—provides unrestricted access to the system.
What That Means
This is the absolute worst-case scenario. The adversary has acquired privileged authority (like administrator access) into a server or computer connected to AFNET. The Adversary is able to transmit sensitive data outward, to keep creeping around the network, or even launch additional attacks against critical mission systems, all from inside AFNET.
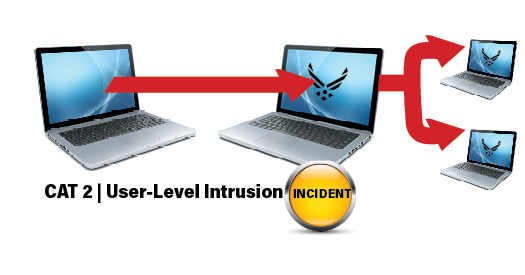
Official Definition
Unauthorized nonprivileged access to an Air Force system. Nonprivileged access—often referred to as user-level access—provides restricted access to the system based on the privileges granted to the user.
What That Means
This is the second worst-case scenario. This time, the adversary has gotten access into a computer connected to AFNET, but without privileged authority (like user access). Adversary can’t do much to this computer, the network, or infrastructure. However, the skill necessary to get this far means the adversary is likely trying to escalate access to the privileged kind.

Official Definition
Deliberate, unsuccessful attempts to gain unauthorized access to an Air Force system that are defeated by normal defensive mechanisms, and the activity cannot be characterized as exploratory.
What That Means
The adversary tried to penetrate AFNET, faced ACD and/or a cyber warrior, and was defeated. Despite the victory, the event must be investigated to figure out what went wrong that allowed a battle in the first place.
The adversary tried to penetrate AFNET, faced ACD and/or a cyber warrior, and was defeated. Despite the victory, the event must be investigated to figure out what went wrong that allowed a battle in the first place
Official Definition
Activity that impairs, impedes, or halts normal functionality of a system or network.
What That Means
USAF considers denial of service attacks grave incidents. The adversary may program a botnet to send so much traffic into a mission-critical network system that the system fails under its weight.
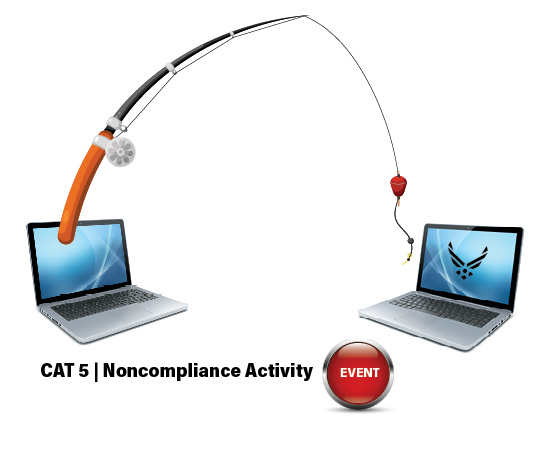
Official Definition
Activity that potentially exposes Air Force systems to increased risk as a result of the action or inaction of authorized users.
What That Means
AFNET-authorized airmen can also be a vulnerability. They may open and click around phishing emails or download infected software into AFNET. Damaging or insecure activity by airmen is extremely common.
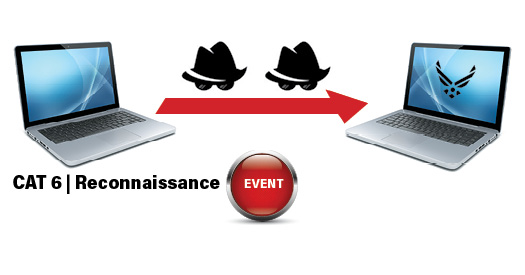
Official Definition
Activity that seeks to gather information used to characterize Air Force systems, applications, networks, and users that may be useful in formulating an attack.
What That Means
Someone’s trying to figure out what AFNET looks like from the inside, mapping it out or tracking it in some way. That someone isn’t necessarily an adversary, and the activity may or may not be malicious. But such knowledge could potentially lead or aid an attack on AFNET.
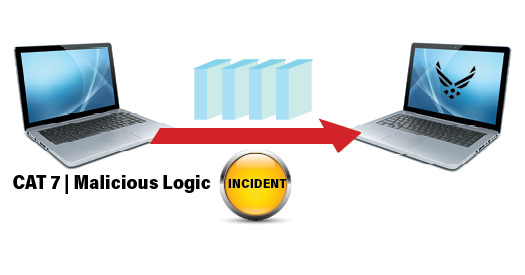
Official Definition
Installation of software designed and-or deployed by adversaries with malicious intentions for the purpose of gaining access to resources or information without consent or knowledge of the end user. This category can be further broken down to moderate and severe.
What That Means
A program or piece of software has made its way into AFNET through a computer or server and is now installed. Whether the logic in the program is designed to carry out an attack on the network or not doesn’t matter—it needs to be dealt with. These usually get into the network without the consent or knowledge of the user who allowed them in, perhaps by opening and clicking around a phishing email.
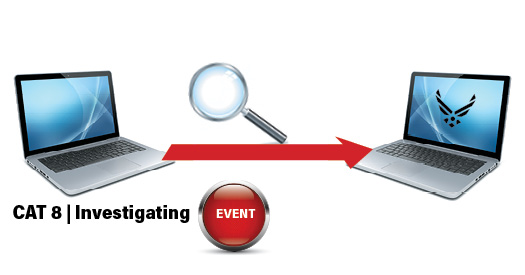
Official Definition
Events that are potentially malicious or anomalous activity deemed suspicious and warrants or is undergoing further review. No event will be closed as a Category 8. Instead, they will be recategorized to the appropriate CAT 1-7 or CAT 9 prior to closure.
What That Means
Without further research, it’s hard for ACD to know what this event signifies, forcing further review. It may fall to the Category 9 realm of little significance or threat, or it may be determined malicious, requiring a more critical categorization
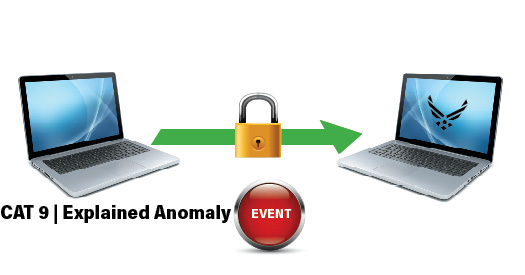
Official Definition
Suspicious events that, after further investigation, are determined to be nonmalicious activity and do not fit the criteria for any other categories.
What That Means
This is benign activity ACD or cyber warriors determine to be nonthreatening. Usually, ACD will be tweaked to recognize this the next time so to not trigger a category description, and maybe even deal with the issue automatically.
To learn more about the ACD, read “Meet USAF’s Most Widely Spread Cyber Weapon System” in the Dec. 1 Daily Report at airforcemag.com.